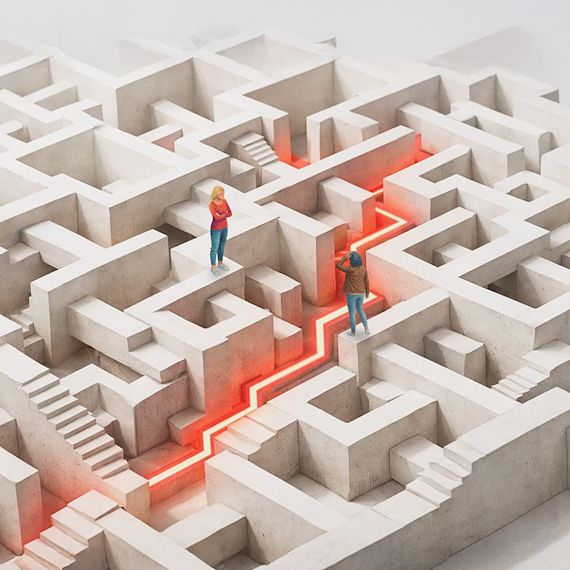
Red Teaming is not a vulnerability scan. It's a controlled, objective-driven simulation that mirrors how real attackers operate gaining initial access, escalating privileges, moving laterally, and targeting crown-jewel assets. We measure not just what's exploitable, but how your organization detects and responds.

The State of Cybersecurity in Australia
Australian companies are being subjected to at least one cyberattack every 7 minutes. Here's what's happening in Australia and how Packetlabs can provide support.
March 25, 2026 - Blog